I woke up a few days ago to a surprise from my team at Batuta, the cybersecurity company I co-founded several years ago. Over the last few months, they have been executing on a side passion of mine, a dream to bring people viscerally and tangibly into the experience of a cyber attack.
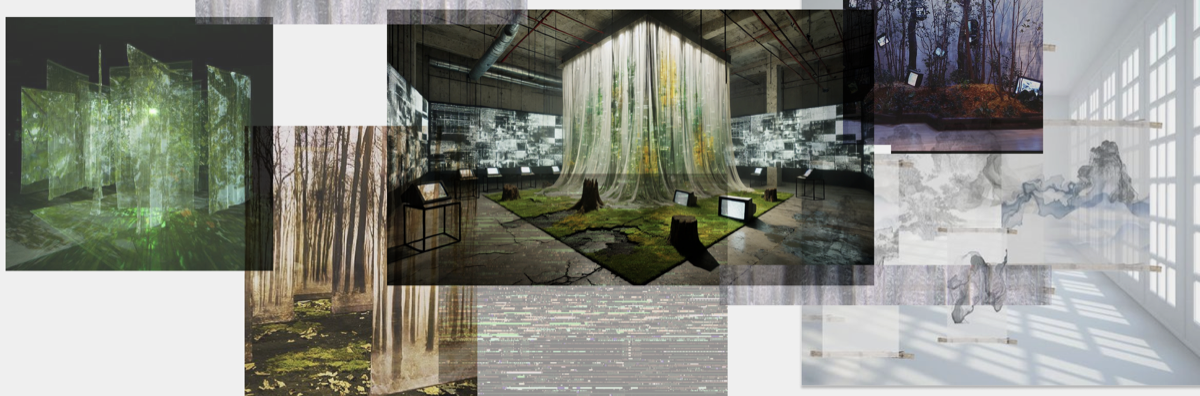
It’s an installation that takes the invisible architecture of an attack and makes it impossible to ignore. A live honeypot lures real-world intrusion attempts, translating them into a soundscape you can feel in your sternum. HTTP flows become slow, steady drumbeats. DNS lookups click. SMB traffic hums until an attack distorts it into something jagged, metallic, almost alive. LED lights and projected visuals flare and dim in sync, the room breathing in time with the assault. What happens when you can no longer ignore what you've been trained not to hear? The installation answers this for networks. My cancer diagnosis answered it for me.
As I sat in the hospital where time stood still, I flipped through their photos and videos. If it had been another year, I would have been in Vegas at Black Hat and Defcon with them, fighting the suffocating heat of the desert and the overwhelm of vendors hawking a new defensive tool. Outside, the world still spins. Technology conferences stop for no man.
It has always fascinated me how much we build our cities, our art, our architecture, our computer systems in the model of ourselves. In the words of Ellen Ullman, “We build our computers the way we build our cities—over time, without a plan, on top of ruins.” The truth is, we build them the way we build ourselves. Layered, flawed, elegant, prone to failure in the same familiar ways. We think we’re inventing, but mostly we’re remembering.
Nothing comes without its world. And the ways we undo those worlds, slipping in quietly, replicating, persisting until collapse, are the same whether the target is silicon or skin. The cancer in me runs the same playbook as a ransomware campaign: hide in plain sight, map the terrain, strike when the system is most exposed. And the countermeasures are brutal by design. My system is flooded with agents that burn everything in their path, good cells and bad, clean code and compromised alike.
But in both cases, there is a sort of eeriness, a quietness. A network under siege hums like it always did. If you saw me on the street, you wouldn’t know the difference. At every point, something is failing. Every second brings both the network and body closer to decline. As the old cybersecurity adage says, “it’s not a case of ‘if’ you get hacked, but ‘when’”.
I think a lot about the sounds we don’t want to hear. The ones we file as background until they force themselves forward. We lower the volume on endings, on decline, on the rhythms of loss. Countless cyber breaches remain unreported globally, and companies avoid investing because they believe it won’t happen to them. We think that if we don’t acknowledge the fallen, we can keep the illusion of uninterrupted life. If a tree falls in the forest and no one hears it, does it still make a sound? Not hearing doesn’t mean it’s not happening; we’re just unprepared for what follows.
Neil deGrasse Tyson once said that when a tree is dying, other trees reach toward it through the roots, sending water, sugar, and sustenance. Trees don’t turn away from the reminder of their end. They move toward it.
Silence is not the absence of change. It is the medium in which change can happen. And to listen, to truly listen, is not to stop the fall, but to be ready for what grows in its place.