I think about safety more than the average person. Safety is something I’ve always been acutely aware of - what feels safe? Is this a safe space? Am I safe?
My obsession with safety and security is a natural precursor to my co-founding a cybersecurity startup, but more than anything, it’s a function of being human in a changing world. We can think the best of human nature, but inevitably, not everyone wishes us well at every moment. Dissent always follows troubled times—be they economic, political, religious, or social in root. In this present era, where a new crisis emerges daily and inevitably, a new debate tears us apart, the inherent assumption that all roads are paved with good intentions becomes harder to believe.
Safety is a human right. Secondary only to the human need for food, water, and shelter is the need for safety.
We optimize for safety in the jobs we take—job security, financial security—in who we marry—stability, and in how we live—safety net. We edit ourselves—we dress out of safety, and to fit in, we adjust our views to align—to be part of a ‘trusted’ group. It’s easy to pick on the Midtown East Patagonia vest-wearing finance bros, but group any ideologically similar group together, and there is inevitably convergence towards a mean.
We inherently (and biologically) trust those who look the most like us, and who share our beliefs, but in this present era where the potential points of bifurcation have expanded, nothing is certain anymore. How do you know who to trust? What is safe?
If we are to zoom out, there are philosophically two approaches to establishing safety: One is more of a macro, prison guard looking in, panopticon approach. The other is a micro, individual code of conduct approach. I, in no way, would advocate for blindly trusting people on the internet - especially when, these days, there tends to be more AI than humans out there. Thus, it is significantly easier to put up defenses and add more security cameras and guards - whether in your physical space or cyberspace. Blackhat, one of the largest cybersecurity conferences, happened last month, and I couldn’t help but be overwhelmed by the new-ness, the new layers and techniques focused on defense, and the new technologies to supplement your just purchased but already obsolete ones.
But, taking ourselves out of the abstract and obtuse realm of cybersecurity and into the real realm of real life, what actually feels safer: a heavily guarded compound with bulletproof windows and layers of security cameras or a clean, well-planned, well-lit, well-maintained park where everything inexplicably just seems to work. Where do you feel most at peace?
What is the difference between these two spaces? It is the difference in how they are controlled. The first creates safety through layers of external defenses, while the second creates safety through underlying control and planning.
There is merit in both, but also execution challenges - they both lead to risk reduction from different angles. Looking from the top down, many defense technologies boost detection rates of 98.5% - but in all likelihood, they’re not uniformly deployed across an organization, leading the true coverage percentage to be closer to 60% (not accounting for multiple layers of coverage or blindspots). From the bottom up, 70% of cybersecurity risk can be reduced with minimal investment through underlying control and planning measures (such as patching, software updates, and password changes). In both approaches, there is always a sense of futility - if you’re dealing with a sophisticated nation-state attacker, it may cost more money and time for them, but there is inevitability always a way to break through your defenses. In physical life and cyber life, there is no way to thwart death and destruction, but there are known ways to prolong the inevitable.
In a layered patchwork of defenses, you have to assume that something will detect irregularities, but you’re left with a second-order challenge of managing alerts and triangulating and correlating response actions. It’s next to impossible to stay current with all the new technologies, let alone ensure they are properly implemented and managed in your organization. The second approach, while more sustainable in the long term, leads to work that is more analogous to being a digital janitor or plumber. It is a tedious organization of IT assets you own and the cybersecurity technologies running on top - updating systems, deploying patches, fighting with your IT department, and receiving hate mail from your sales team and leadership because of your mandatory password changes. Much like a janitor or a plumber, it is a function we all need but are all reluctant to do.
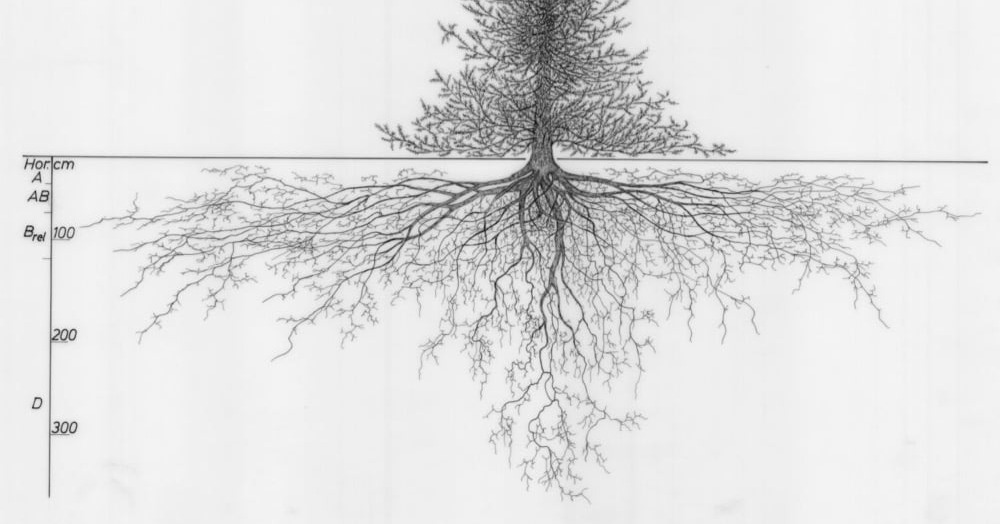
It sounds trite to say, but we are all humans. It is easy to be wooed by the shiny newness of a novel defense, a new technology. We constantly seek new - AI, quantum computing, crypto, space travel - but we forget that new is inevitably built upon the base of what has come before. To quote Ellen Ullman, “We build our computers the way we build our cities—over time, without a plan, on top of ruins.”
Is it a mindset shift? What if we valued the digital janitor/plumber archetype as much as we do the cutting-edge technologist/hacker in popular culture? What if we sought to fix what we have—our planet, our computer networks, our legacy systems, our infrastructure—rather than focusing only on what’s new?
The cracks in the foundation of our cybersecurity programs are starting to show.
My Wake Up Call
Years ago, I read an article that fundamentally changed my life. I couldn’t even finish it when I first saw it because I was so upset. In the 1970s, the government commissioned a report, The Ware Report, which I realized, upon reading, detailed many cybersecurity vulnerabilities that we still have today. In the fifty years since publishing and the thousands of cybersecurity companies created, we have not solved our core problems. And if we are being truly cynical, many of these problems are inherently unsolvable due to our prioritization of connectivity. Moreover, the security of our systems is reliant on our IT foundational base.
I have forever been a sci-fi aficionado. I came to age alongside Nell from Stephenson’s Diamond Age, I shaped my view of digital connectivity rooted in human interaction from Vinge’s Rainbow’s End. I’m a forever optimist. I think the best of mankind and people. I’ve always dreamed of building virtual worlds, of building connections based on something greater than just physical, of exploring spaces beyond what exists in our known world. But I realized in that moment that this dream was fraught. It would be impossible to reach the level of connectivity in a virtual world that I wanted without security in the system.
At that moment, I realized my Sisyphusian challenge: the absurdity and the challenge of safe spaces. Creating them is the purpose of my life, my modus operandi.
In Search For The Holy Grail
I mentioned a few paragraphs ago that approximately 70% of cybersecurity attacks could be prevented with minimal investment. But why aren’t they? What is the nature of those 70% of attacks, and how could they be prevented? More importantly, what makes this difficult?
I tend to find that most articles and reports on cybersecurity use an abundance of acronyms and technical jargon, so I’m attempting not to repeat the same here. At the risk of oversimplification, I’ll attempt to distill a few key points to reach a broader audience of understanding.
1. The Majority of Cyber Attacks Are Not Targeted :
* One of the most significant challenges in cybersecurity has always been the asymmetrical advantages of attackers. If you were alive during the 90s, you may have been lured by the prospect of a great fortune from a Nigerian Prince. It is incredibly easy to send emails en masse, and equally easy to target multiple networks from one computer. You just need one person to click a button, and one person out of thousands to fall for it. Attack techniques have progressed to where you don’t even need a person in the middle - all you need is the ability to scan networks and devices to look for potential holes automatically. It has gotten significantly easier over time - attackers can scan the entire internet in minutes.
* Back to the point that we are all human - most attackers think about ROI (return on investment), too. It is cheap (almost free) to focus first on these easy targets - unpatched systems, passwords that haven’t been updated - more inevitability than not, you will catch a whale. We talk a lot about the risk of AI and quantum computing in cybersecurity, but the reality is, in a world where we leave unpatched systems online, there are significantly easier ways to break in
2. It’s Difficult To Keep Track of What You Have (and Even Harder To Ensure That What You Have Is Protected):
* The first point of almost every cybersecurity framework is the same: Inventory. Yet few companies truly have complete certainty in exactly what they own. It’s easy to see how quickly things can go awry - a decommissioned server that was never fully taken offline, a new cloud instance sprung up by an intern, new employees, remote work, temporary contractor access. Inventory begets visibility which begets control.
* The problem compounds when you add in the technology you’ve deployed on top - you’ve purchased 2,000 licenses of [insert your preferred endpoint cybersecurity technology here], but how do you know for sure those agents are properly installed and configured across all of your devices? Multiple this problem if you have subsidiaries with different technology stacks. Multiple it again if you’re on an acquiring spree. Few companies have certainty in this matter.
3. It’s Everyone’s Problem and No One’s Problem:
* One of the biggest challenges to maintaining secure networks falls between two departments - IT Operations and Cybersecurity. Every company has its own system for patching devices (maintaining system updates), but it usually falls to the asset owner. From a business perspective, it’s clear - you know where your crown jewels are, and you protect them. And more likely than not, multiple assets just aren’t that relevant to you. And if we’re being honest, their owners probably left the company years ago, and that server has just always been ‘there’. From an attacker view - an asset on your network is an asset on your network. It’s an opportunity to get in, to move laterally, to continue to find holes. There is a fundamental disconnect between how most businesses operate and what they need to do to be secure.
I co-founded Metabase Q years ago based on my desire to make it easier for any company to eliminate the majority of its cyber risk through fundamental and proactive cybersecurity measures. To create a safe space, you have to start with the foundation. Our platform, Batuta—Spanish for ‘conductor’s wand’—is a control plane for Security Operations, enabling centralized management of assets and cybersecurity technologies. It’s a cloud-native endpoint management platform.
We created this product because of the problems we saw across our customer base and our concerns when managing their security. Few companies knew their complete inventory. Almost no one could say with certainty that the technology they had spent millions of dollars on was working - uniformly deployed and phoning home - as it should be.
These are boring problems but massive ones that dramatically reduce the cyber risk of any organization.
It’s always scary as an entrepreneur to tie yourself too closely to your company, so I intentionally have tried not to for years. That said, this is a problem I care deeply about and one that hits the deepest part of my core. I believe in a techno-optimistic future where greater human connection is enabled through digital connection, but the online worlds we live in today are not as safe as we think. I believe this is possible to change, and I believe it starts with a re-focus of priorities. In the world we live in of broken pipes, doors, and windows, we need digital janitors/plumbers.
Note: This personal note sheds some light on my founder journey. All views expressed belong solely to me.